Wifi Hacking
tags: #presentation, #hacking
WiFi Bandwidth
- 2.4 GHz
- 5 GHz
WiFi Standards
- WEP (terribly insecure)
- WPA/WPA2 (most common)
- WPA3 (latest standard)
WEP
60 bit or 128 bit encryption key = IV (initialization vector) = RC4 key
Vulnerability in the IVs being reused
Guaranteed compromise with 5 mins capture
WEP hacking

- interface monitor mode with
airmon-ng
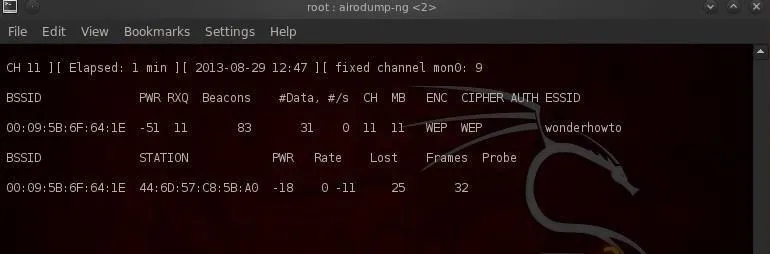
2. capture WEP AP packets, check for roughly 5000 IVs
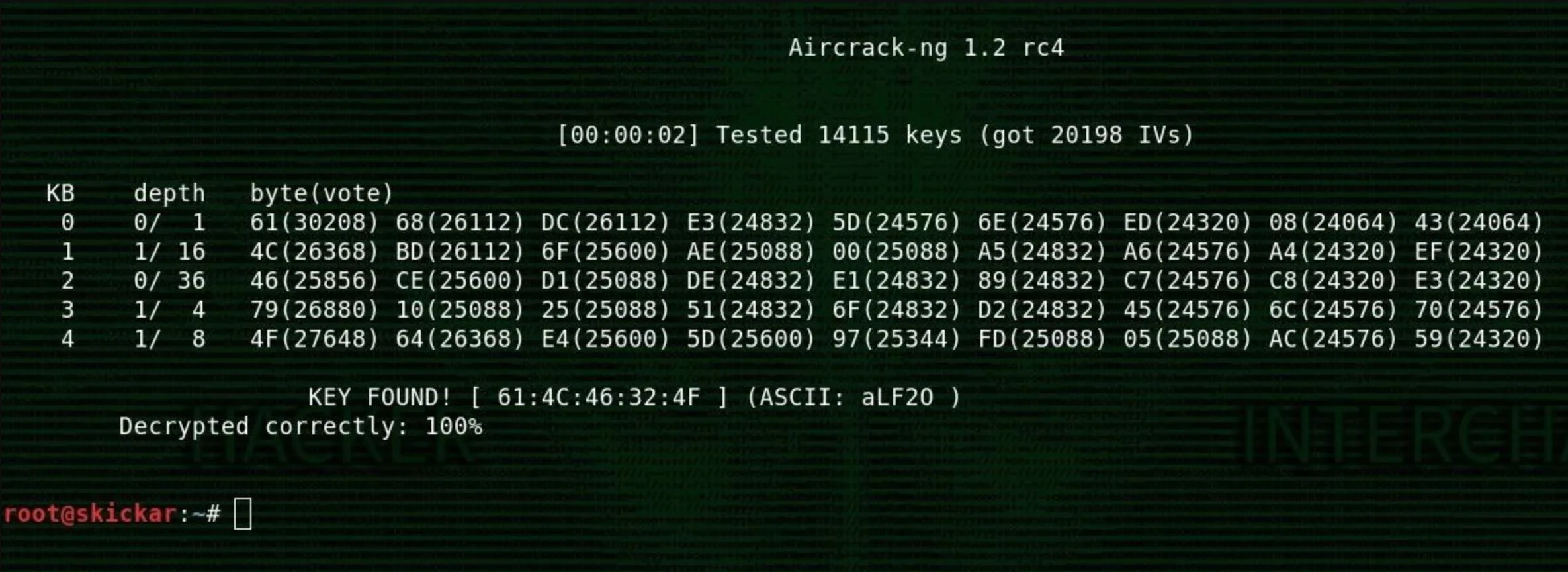
3. crack with aircrack-ng
WPA/WPA2
Vulnerability lies in the handshake packets
The handshake packets can be captured and bruteforced
Steps
- Monitor mode on interface
- capture packets from AP
- De-auth the connected clients, force handshake
- Crack handshake with wordlist
WPS
WPS Pin = 8 digit number (fixed)
Steps
- Monitor mode on interface
- use
reaver, start bruteforcing pins - Using pin to recover current password
Other Wireless Attacks
- Broadcasting thousands of beacons
- kick someone out of wifi by deauth
- forcing people to connect to you
Tools
- aircrack-ng (most classic)
- reaver
- pixie dust
- wifite